Active Directory penetration testing utilizes a variety of offensive cybersecurity and networking tools. Common tools used in Active Directory include Bloodhound, PowerView, Impacket, Rubeus, and Metasploit. Crackmapexec (cme) is another popular tool that can be used throughout a penetration test but is technically described as a post-exploitation tool. The official CME wiki can be found here.
CME is run by Porchetta Industries, which has a paid version with extra modules, but a free version is also available on GitHub.
CME currently can be used with the following protocols: SMB, MSSQL, SSH, FTP, WINRM, LDAP and RDP. CME has a variety of modules and options that can be used with these protocols during a penetration test, and they typically work well with proxy tools like proxychains. A quick way to check for available modules for each protocol is with –L:
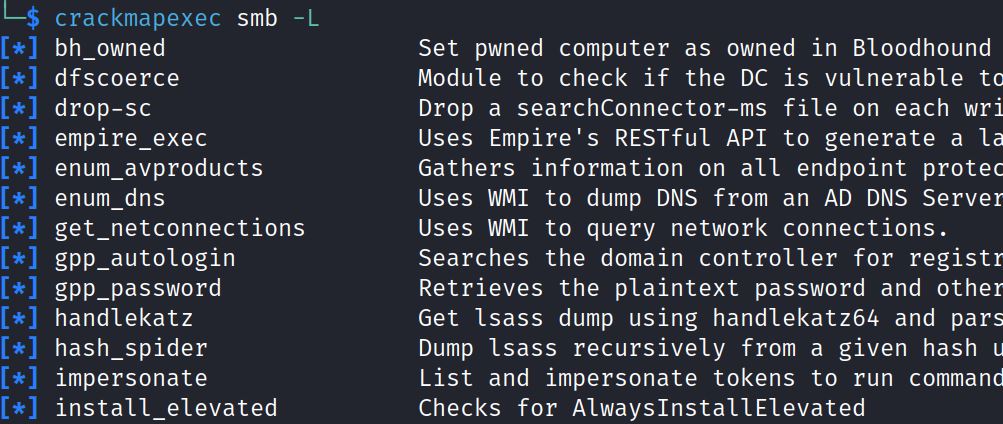
This post aims to highlight some popular CME modules and options for Active Directory penetration testing, but there are many more options available so make sure to check the wiki or use –L to get a full range of options!
Acknowledgement: many of the module descriptions come largely from the CME GitHub page mentioned above. Final note- cme options use two dashes (-), and modules use one dash (-), formatting below may not show this.
Reconnaissance
1) Check Guest or Anonymous SMB Share Access
cme smb <IP> -u ‘’ -p ‘’
cme smb <IP> -u ‘a’ -p ‘’
2) Password Spray: FTP, SSH, RDP, MSSQL, WINRM
cme <protocol> <IP> -u <users.txt> -p <passwords.txt> –no-brutefore
CME also includes the –-continue-on-success flag, to ensure CME doesn’t stop after a valid password is found. Hydra is typically a better tool to test some of these services, like RDP.
3) Enumerate Hosts with SMB Signing Not Required
cme smb <IP-List> –gen-relay-list relaylist.txt
This maps the network and saves hosts that do not require SMB signing into an IP list, e.g. “relaylist.txt”. An attacker could then attempt an NTLM relay attack using tools like Responder and Impacket’s ntlmrelayx.py.
Initial Access
4) Authentication and Command Execution
CME can be used to confirm authentication for SMB, MSSQL, SSH, FTP, WINRM, LDAP and RDP.
CME includes the –-local-auth option for attempting local logon.
If there is local admin access, CME includes (Pwn3d!) which means the credentials could be used for initial access. CME also includes command execution for many of these protocols, even MSSQL with xp_cmdshell.
5) SMB Enumeration with Valid Credentials
- List shares: –shares
- User password policy: –pass-pol
- List user: –users
- Spider shares: –spider
- List and dump all files from readable shares into a file: -M spider_plus
6) Upload and Download Files with SMB and MSSQL
CME can be used to upload and download files with SMB and MSSQL.
Both protocols use the same format:
–put-file </localpath/file.txt> <\\remotepath\\file.txt>
–get-file <\\remotepath\\file.txt> </localpath/file.txt>
7) Use SMB to check for Common Vulnerabilities And Services
- “ZeroLogon” (CVE-2020-1472): –M zerologon
- “PetitPotam” (CVE-2022-26925): -M petitpotam
- “noPac” (CVE-2021-42287): -M nopac
- GroupPolicyPreferences: -M gpp_password: Retrieves the plaintext password and other information for accounts pushed through Group Policy Preferences. -M gpp_autologin: Searches the domain controller for registry.xml to find autologon information and returns the username and password.
- WebDav: -M webdav and –M drop-sc
webdav: Checks whether the WebClient service is running on the target. drop-sc: Drop a searchConnector-ms file on each writable share to remotely coerce a host to start WebClient service.
Print Spooler: -M spooler
Detect if print spooler is enabled or not. This is for the “PrintNightmare” vulnerability.Exploit SMB share (coerce SMB)
CME has two modules –M slinky and –M scuffy that target writable SMB shares.
-M slinky: Creates windows shortcuts with the icon attribute containing a UNC path to the specified SMB server in all shares with write permissions
-M scuffy: Creates and dumps an arbitrary .scf file with the icon property containing a UNC path to the declared SMB server against all writeable shares
I haven’t used these two modules, but two helpful resources are swisskeyrepo and this post.AlwaysInstallElevated: -M install_elevated CME checks for AlwaysInstallElevated, which can lead to privilege escalation by changing a writable MSI package.
8) Check DACL Rights and use Bloodhound Ingestor
- CME’s LDAP includes -M daclread, which allows for reading the DiscretionaryAccessControlLists (DACLs) of AD objects.
One example, from the wiki, shows searching for DCSync rights on the domain:
-M daclread -o TARGET_DN=”DC=lab,DC=LOCAL” ACTION=read RIGHTS=DCSync - CME also has a new feature that ingests data found through CME into BloodHound. This can be done by updating the cme config file and also using the “–-bloundhound –-ns <IP> –-collection all” option to output into a ZIP file.
9) Target LAPS, gMSA, MSSQL, ADCS, Impersonate Tokens
- Check if user can read LAPS password through smb or winrm: –laps
- Extract the password of a gMSA account through ldap: –gmsa
- Enumerate MSSQL privileges and exploit them: -M mssql_priv
- Find PKI Enrollment Services in Active Directory and Certificate Templates Names through ldap: –M adcs
- List and impersonate tokens to run command as locally logged on users through SMB: -M impersonate
Local Administrator and/or Domain Admin Access
An attacker with admin access could go back and use the previous modules. As an admin they can also dump credentials, which will depend on local or domain admin access, and access to the Domain Controller.
10) Dump Credentials
Requires at least local admin privilege on remote target, can use –local-auth for local account:
- Extra from SAM: –-sam This requires local admin and can include –local-auth.
- Extra from LSASS: –-lssasy
There are also credential modules like: wireless, keepass, and DPAPI.
Requires local or domain admin on DC:
- Extra from LSA: –-lsa
- Extra from NTDS.dit: –ntds

