Introducing and Setting Up the New Kali Linux 2023.1: Kali Purple
Table of Contents
Kali Purple Features
Today, Kali Linux’s 10-year anniversary, Kali Linux released their newest Kali Linux version: Kali Purple. Kali Linux is known for specializing on offensive security and providing hundreds of red team and pen testing packages and tools. Kali Purple aims to bridge the gap between red team and blue team by providing a host of new capabilities. As they describe it, Kali Purple is the “one stop shop for blue and purple Teams” and the “ultimate SOC In-A-Box“. In this post I’ll explain how to install Kali Purple and review some Linux command line syntax.
Kali Purple includes over 100 blue team or defensive tools for capture analysis, vulnerability scanning, incident response and detection. Some include:
Arkime – Full packet capture and analysis
CyberChef – The cyber swiss army knife
Elastic Security – Security Information and Event Management
GVM – Vulnerability scanner
TheHive – Incident response platform
Suricata – Intrusion Detection System
Zeek – Intrusion Detection System
Kali Purple includes Python 3.11 along with new options for downloading packages, including venv. More information on kernel settings, Kali ARM updates and new tools can be found here.
There are two ways to set up Kali Purple. You can update from an existing Kali install or download a new installation image from kali.org.
Method 1: Update From an Existing Kali Install
Here are the four steps for updating to Kali Purple. I’ve also included a walkthrough at the end which explains the commands and minor issues that can come up during the update process.
- echo “deb http://http.kali.org/kali kali-rolling main contrib non-free non-free-firmware” | sudo tee /etc/apt/sources.list
- sudo apt update && sudo apt -y full-upgrade
- cp -vrbi /etc/skel/. ~/
- [ -f /var/run/reboot-required ] && sudo reboot –f
Method 2: Installing Direct From Kali.org
You can get Kali Purple on the main page here: https://www.kali.org/get-kali/
Note: If you click sum on the bottom right it provides the file hash:
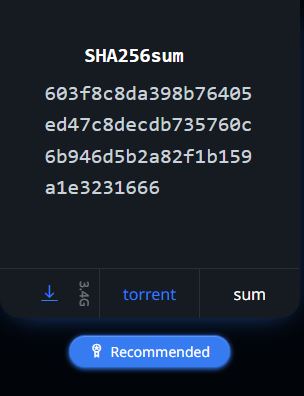
After downloading the file you can compare the file’s hash with sha256sum to make sure they match: sha256sum <file>
Updating to Kali Purple Walkthrough
echo “deb http://http.kali.org/kali kali-rolling main contrib non-free non-free-firmware” | sudo tee /etc/apt/sources.list
The echo command is used to send a display of text. In this case, it is a string of text which includes a HTTP link to the Debian distribution kali-rolling. The tee command accepts the echo string output and writes it into the source.list file:
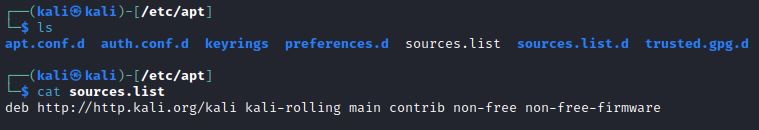
“deb” is not a command, it declares that this is a Debian distribution data source in the source.list file.
As google explains:
The file /etc/apt/sources.list contains a list of configured APT (Advanced Package Tool) data sources to fetch packages from the Internet or local repository on a Debian or Ubuntu Linux based system
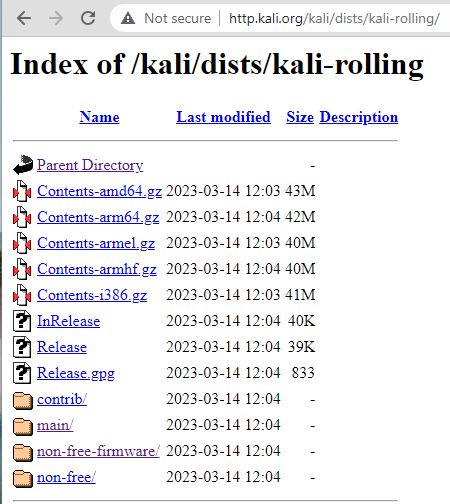
So, you are declaring the Debian archive location for where to download this Debian distribution. You’ll notice that there are spaces after the HTTP link. These designate the sub-sections of the archive and provide the path for further components to download. This distribution is kali-rolling, and the components are: main, contrib, non-free, non-free-firmware:
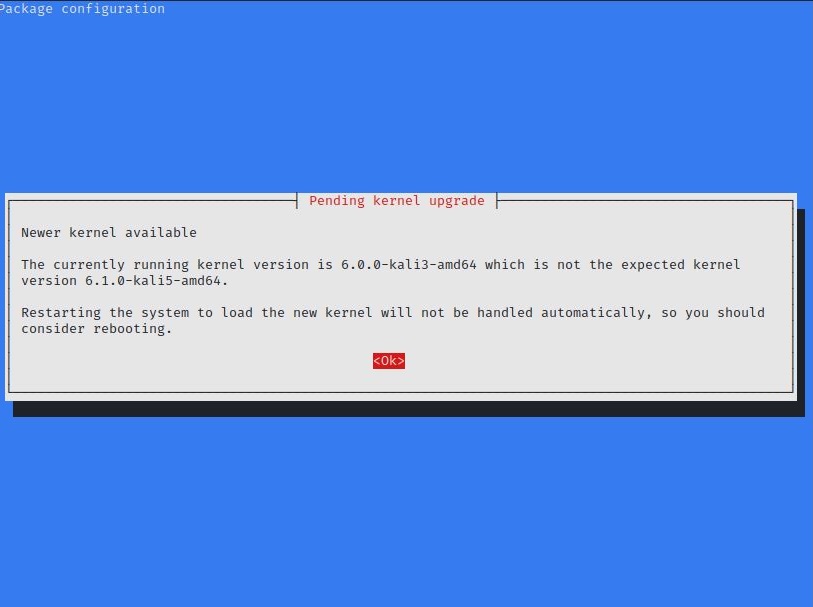
You will likely get Kernel and processor updates. Click OK to continue. Other prompts may ask if you want to update packages and binaries. You can use the Tab key to navigate, Space Bar to select, and Enter key to continue.
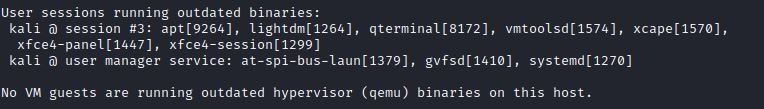
Note you will also likely get warning messages showing you have outdated binaries like this one at the end of the update:
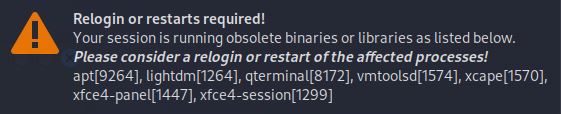
Or an alert showing outdated binaries:
These outdated binaries alerts are fixed in the second step:
sudo apt update && sudo apt -y full-upgrade
This updates available packages and then upgrades these software packages. The “full-upgrade” option removes old packages as needed to perform upgrades of new packages. The more common “upgrade” option skips updating packages if removing old packages is required to update.
cp -vrbi /etc/skel/. ~/
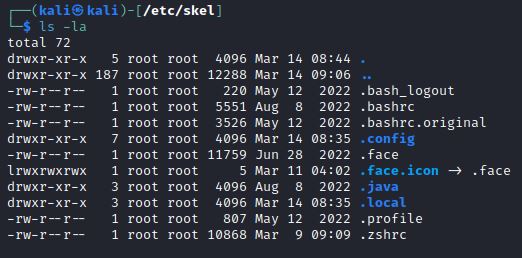
This is a copy (cp) command that includes: verbose (-v), recursive(-r), interactive(-i) and backup(-b) options for the files in /etc/skel/. The /etc/skel directory contains files and directories that are automatically copied over to a new user’s home directory. The hidden files in /etc/skel can be seen with the command ls –la:
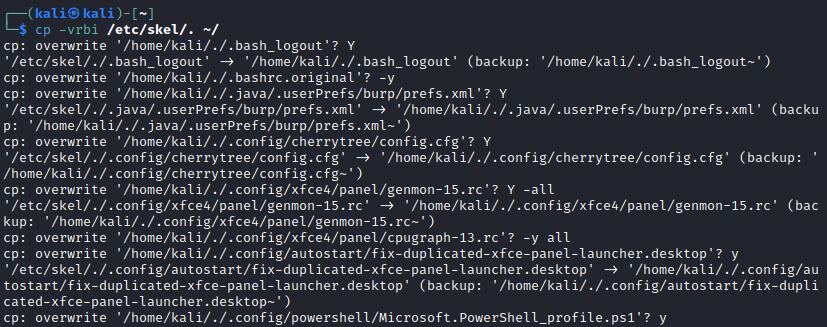
By using the recursive and interactive options with the copy command, you are recursively copying all these files and prompted before you can overwrite them in the user’s home directory: ~/
This interactive option leads to various prompts to confirm overwriting your home directory. You can answer each prompt with a Y for yes:
The final command conducts a reboot:
[ -f /var/run/reboot-required ] && sudo reboot -f
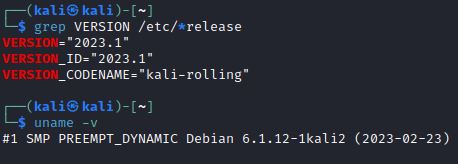
After the reboot you check your new Kali Linux distribution version:
grep VERSION /etc/os-release
uname –v
uname -r